CVE-2025-14812: Zero-Click Address Bar Spoofing in Arc Browser iOS

Assalamualaikum, my name is Syarif Muhammad Sajjad, also known as syarif07 on HackerOne.
In this writeup, I’ll walk through one of my findings that was assigned CVE-2025-14812, a high-severity vulnerability in Arc Search for iOS that enables zero-click address bar spoofing.
TL;DR
Arc Search for iOS failed to correctly track the top-level browsing context origin in its address bar when an embedded iframe triggered a navigation to a mobile URI scheme such as geo: (custom URI). The result: the omnibox would update to display the iframe's origin an attacker-controlled domain while the visible page content remained unchanged from the original site. Users were shown a domain they never navigated to.
Vulnerability Details
Root cause
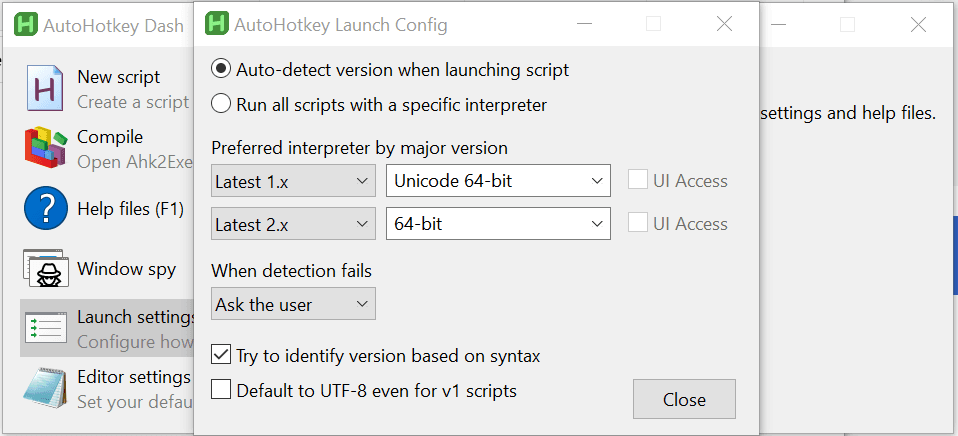
When Arc Search iOS encountered a URI-scheme navigation (geo:, tel:, sms:, etc.) originating from an iframe, it incorrectly treated the iframe's origin as the new top-level origin and reflected it in the address bar. The top-level document never navigated only the subframe did, to a non-HTTP scheme but Arc's navigation delegate updated the omnibox as if the whole page had changed.
This is a browsing context origin misattribution bug. The fix: the address bar should only ever reflect the top-level browsing context URL. Navigation events from subframes, especially to URI schemes that don't produce a visible page, must not propagate to the omnibox.
Notably, Arc macOS was unaffected it correctly retained the top-level origin throughout. The bug was specific to how the iOS build wired up its WKWebView navigation delegate.
Why it's zero-click
The iframe fires on page load with no user interaction required. Simply visiting the attacker's page is enough to trigger the spoofed address bar state. This is what drove the severity upgrade from Medium to High during triage.
When the victim page loads in Arc Search iOS, the iframe automatically fires the geo: navigation. Arc's navigation delegate misattributes the iframe's origin as the top-level origin and updates the omnibox to attacker.github.io while victim.com's DOM remains fully visible on screen.
The original PoC used Glitch.me, which later shut down. The researcher updated it to use GitHub Pages, which is significant: a real-world attacker could register a convincing lookalike domain and host the redirect script there.
Impact
The spoofed domain shown in the address bar is the iframe's domain the attacker can only display a domain they control. This means the attack doesn't directly let someone fake paypal.com unless they can get the geo: redirect script hosted on a PayPal subdomain (e.g., via an open redirect). However, several scenarios remain viable:
Lookalike domain phishing. The attacker registers paypa1-support.com, hosts the geo: script there, and iframes it inside a legitimate-looking page. The mobile address bar (already space-constrained) shows paypa1-support.com as the apparent origin while a convincing phishing form fills the viewport.
Social engineering with trusted sub-contexts. On mobile, users heavily rely on the address bar for trust signals. Showing any unexpected domain even one clearly controlled by an attacker undermines the user's ability to know what site they are on.
Permission prompt abuse. The geo:, tel:, and sms: URI schemes can initiate system-level prompts. Triggering these while the address bar shows a different, possibly trusted origin creates confusion about what is requesting the permission.
Timeline
| Date | Event |
|---|---|
| Jun 17, 2025 | Initial report submitted to HackerOne |
| Jul 8, 2025 | Triaged as Medium |
| Oct 9, 2025 | Severity upgraded to High after zero-click nature confirmed; bounty awarded |
| Dec 1, 2025 | Fix confirmed by researcher |
| Dec 19, 2025 | CVE-2025-14812 published |
The Medium → High reclassification came down to one realization: the iframe fires automatically on page load, requiring zero user interaction beyond visiting the page. That single fact moved the CVSS UI metric from R (required) to N (none), explaining most of the score increase.
Remediation
Update Arc Search iOS to version 1.45.2 or later. The fix prevents subframe URI-scheme navigation events from propagating to and updating the top-level omnibox origin display.
Credit: syarif07, reported through The Browser Company's vulnerability rewards program.

![[Bug Bounty] Race Condition: Redeeming Single-Use Coupon Multiple Times](/_next/image?url=https%3A%2F%2Fcdn.hashnode.com%2Fres%2Fhashnode%2Fimage%2Fupload%2Fv1770116456998%2F629ff44d-4a0a-4445-91bf-c37d3e84c104.jpeg&w=3840&q=75)